If you want a boots-on-the-ground measure of container interest and adoption, check in with the people who actually write your code.
When DigitalOcean did just that in a recent survey of nearly 5,000 software developers, it found almost half (49 percent) are already using containers today. Of those not yet working with containers, 78 percent said they plan to in the future. And while 40 percent of those already running containers are doing so only in dev or test environments, we’re moving past the tinker-and-experiment phase: The other 60 percent say they’re working with them in production, too.
[ Struggling to explain containers to non-techies? Read also: How to explain containers in plain English. ]
As container adoption rises – and especially as more companies begin to deploy them to production environments and run them at scale – there’s a corresponding set of trends that CIOs and their teams should have on their radar. We asked a wide range of IT leaders and experts for their input on the top developments to watch in the container universe. Here’s what you need to know.
1. Increased deployment velocity creates increased pressure to automate
Faster, more frequent code releases is a pitch most IT leaders can get on board with; it’s a story the CEO usually loves, too. But that increased velocity has impacts throughout the delivery pipeline, and failing to account for those will cause containerization initiatives to stall.
“As companies move toward containerized applications, their deployment velocity tends to dramatically increase,” says Nick Durkin, senior director of sales engineering at Harness. “While they put tools to handle the increased velocity, companies often forget the impact those tools have on testing, monitoring, and operations teams.”
As more companies begin running and scaling containers in production environments, the case for increasing automation becomes more urgent in those organizations.
“Traditional manual approaches are comprised of time elements that are un-compressible when done by humans, and these easily become bottlenecks,” Durkin says. “There is true value not only in orchestrating the deployment of containers, but more importantly, in automating the verification of the health and success of every deployment.”
2. Containers and orchestration enable the next phases of hybrid cloud and multi-cloud
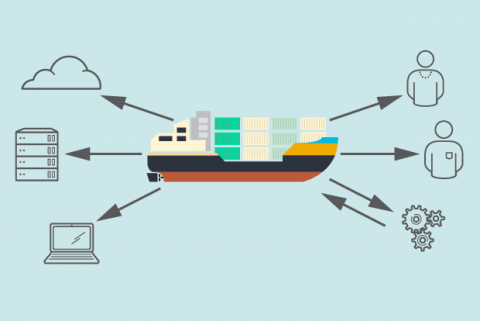
Much of the buzz around containers has been about their promise of portability in an age when enterprise computing is increasingly distributed. That potential could soon be one of the more significant, widespread use cases for containers and container orchestration.
“The biggest trend in container deployments today is the use of orchestration platforms, such as Kubernetes, to aid in building out hybrid and multi-cloud environments,” says Glenn Sullivan, co-founder of SnapRoute. According to Sullivan, most enterprises are indeed eager to embrace the cloud but not so gung-ho on moving all of their workloads into a public cloud and letting their on-premises infrastructure collect cobwebs. Rather, they want to diversify their investments – and containers and container orchestration will increasingly be among the fundamentals that enable them to do so.
“A strategic hybrid cloud model requires organizations to invest in their private clouds and data centers while moving the workloads that make sense into the cloud,” Sullivan says. “This concept of managing both public and private clouds in the same manner is well-defined in the cloud-native movement. The adoption of Kubernetes and other cloud-native tools is leading infrastructure into a new DevOps era where common practices and toolchains can be used to manage all aspects of the modern data center.”
Growing containers adoption will effectively help the theoretical benefits of hybrid cloud and multi-cloud become more attainable for more organizations.
“Multi-cloud and hybrid cloud are gaining momentum on the enterprise CIO agenda, not just to avoid cloud provider lock-in, but as a strategy to push their organizations into a permanent mindset of cloud-native agility and flexibility,” says Amir Jerbi, CTO at Aqua Security. “Containers, being portable by nature, are a pivotal component in making that transition happen and are therefore starting to get that ‘ top-down’ push in addition to the ‘bottom-up’ push they’ve been getting from DevOps teams.”
[ Stuck on your multi-cloud strategy? Read also: Multi-cloud strategy: How to get started. ]
3. Open source communities continue to thrive around containers
“The ecosystem around containers is growing at an incredible pace,” says Ian McClarty, president and CEO at PhoenixNAP Global IT Solutions. “The current leader is Kubernetes, which delivers the most powerful container orchestration system.”
Kubernetes is the prime example of a broader trend in the container ecosystem. Much of its growth can be attributed to open source projects and communities.
“What we are hearing and seeing these days is [that] container users are starting to move up in the maturity curve in terms of the use cases, from picking the right orchestrator – Kubernetes is the winner, no surprise – to picking the right technology around Kubernetes to run containerized applications in production,” says Enlin Xu, director of advanced engineering, Turbonomic.
As IT leaders and teams begin to dig into the realities of running containers in production, Xu says they’re asking sharp questions around monitoring, running stateful application, leveraging service meshes, application performance, and so forth. This is helping to fuel enthusiasm not just around Kubernetes, but several other open-source projects.
Xu points to Istio, Prometheus, and Container Storage Interface (CSI) as three open source projects (in addition to Kubernetes, of course) drawing increasing interest as container adoption grows.