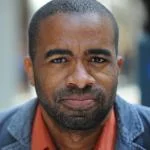
New leaders in government and in enterprise companies have the intimidating task of assessing and protecting against potential security leaks. BitSight executive and former Homeland Security staff director Jake Olcott shares how governments can tackle cybersecurity – and what all tech leaders can learn from their process.

The Enterprisers Project (TEP): How is government security more complex than, say, a decade ago?
 Jake Olcott: One of the key differences between now and 10 years ago is that there is much more visibility into the cybersecurity problem. To paraphrase an old story, someone comes up to a general and says, “We should buy this intrusion detection system. It will give us better visibility into what’s happening on our network.” The general says, “Let’s buy it.” The next day, the guy says “General, it turns out the Chinese are hacking our network and the Russians are, too!” He responds, “It’s because of the stupid network you put on there.”
Jake Olcott: One of the key differences between now and 10 years ago is that there is much more visibility into the cybersecurity problem. To paraphrase an old story, someone comes up to a general and says, “We should buy this intrusion detection system. It will give us better visibility into what’s happening on our network.” The general says, “Let’s buy it.” The next day, the guy says “General, it turns out the Chinese are hacking our network and the Russians are, too!” He responds, “It’s because of the stupid network you put on there.”
In the U.S. government, we’ve gone from a posture of not really knowing much of what was actually happening on the network, specifically civilian, non-Department Of Defense networks, and there has been a massive investment to buy the tools, build processes, and identify malicious networking activities – that’s the whole idea behind the multi-billion dollar Continuous Diagnostics and Mitigation initiative.
Government is getting better at visibility of its own environment, but those environments are dynamic and the attack surface is expanding, too – you can get better at protecting your own networks, but the government relies on third parties and contractors to manage operations and to work on sensitive products. So the attack surface has expanded, as many don’t work in government networks.
TEP: What is the best first step a new government should take to become more secure?
Olcott: That's a great question and a hard one to answer. For any new administration coming in, you have a limited amount of time, energy, and effort, and you need to spend it protecting the most sensitive information. It is important to examine a previous list of critical information and make sure that your own or make a quick review of the most important data we have. Step one is deciding most important information. Step two is knowing where it is. Sometimes it is on government networks, sometimes it's somewhere in the supply chain. You need a strategy to protect that most sensitive data, no matter where it is.
TEP: Will the Internet of Things explosion increase or decrease security opportunities in the government sector?
Olcott: The government is obviously a pretty large beast – very difficult to turn a huge bureaucracy on a dime, so the thought that U.S. government would be in the position to drive leadership on IoT security issues is less likely to happen. There are pockets of government expertise where people are working hard to set the stage, like the FDA in recent years has been focused on cybersecurity of medical devices. How different department and agencies handle cybersecurity differs, and there is no reason to think government as a whole can manage their thinking better than the private sector, which is also struggling.
TEP: When it comes to security, what is the No. 1 mistake governments make?
Olcott: Not treating security as an executive level issue – treating IT cybersecurity as something that the tech people are responsible for rather than the senior executives in the department or agency. In the private sector, there is a growing realization that CEOs, CFOs, general counsels, and boards have shared responsibility for the cybersecurity of the organization. That’s a change – 10 years ago, when people asked about cybersecurity, leaders would say, “That’s what my IT guys do.” Now companies realize it is a really important initiative: “Our rep is on the line, and if we mess this up, we can fail as a company.”
From a government perspective, most seniors or cabinet level secretaries don’t necessarily feel that way about their department. A recent executive order had a big senior accountability for cyber, which is a great start.